May 16, 2013
All Your Skype Are Belong To Us
It's confirmed -- Skype is revealing traffic to Microsoft.
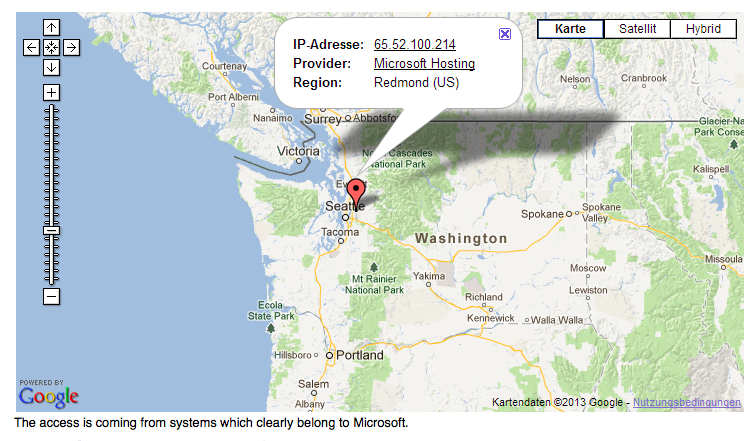
A reader informed heise Security that he had observed some unusual network traffic following a Skype instant messaging conversation. The server indicated a potential replay attack. It turned out that an IP address which traced back to Microsoft had accessed the HTTPS URLs previously transmitted over Skype. Heise Security then reproduced the events by sending two test HTTPS URLs, one containing login information and one pointing to a private cloud-based file-sharing service. A few hours after their Skype messages, they observed the following in the server log:65.52.100.214 - - [30/Apr/2013:19:28:32 +0200]
"HEAD /.../login.html?user=tbtest&password=geheim HTTP/1.1"Utrace map
Zoom The access is coming from systems which clearly belong to Microsoft.
Source: Utrace They too had received visits to each of the HTTPS URLs transmitted over Skype from an IP address registered to Microsoft in Redmond. URLs pointing to encrypted web pages frequently contain unique session data or other confidential information. HTTP URLs, by contrast, were not accessed. In visiting these pages, Microsoft made use of both the login information and the specially created URL for a private cloud-based file-sharing service.
Now, the boys & girls at Heise are switched-on, unlike their counterparts on the eastern side of the pond. Notwithstanding, Adam Back of hashcash fame has confirmed the basics: URLs he sent to me over skype were picked up and probed by Microsoft.
What's going on? Microsoft commented:
In response to an enquiry from heise Security, Skype referred them to a passage from its data protection policy:"Skype may use automated scanning within Instant Messages and SMS to (a) identify suspected spam and/or (b) identify URLs that have been previously flagged as spam, fraud, or phishing links."
A spokesman for the company confirmed that it scans messages to filter out spam and phishing websites.
Which means Microsoft can scan ALL messages to ANYONE. Which means they are likely fed into Echelon, either already, or just as soon as someone in the NSA calls in some favours. 10 minutes later they'll be realtimed to support, and from thence to datamining because they're pissed that google's beating the hell out of Microsoft on the Nasdaq.
Game over?
Or exaggeration? It's just fine and dandy as all the NSA are interested in is matching the URLs to jihadist websites. I don't care so much for the towelheads. But, from the manual of citizen control comes this warning:
First they came for the jihadists,
and I didn't speak out because I wasn't a jihadist.Then they came for the cypherpunks,
and I didn't speak out because I wasn't a cypherpunk.Then they came for the bloggers,
and I didn't speak out because I wasn't a blogger.Then they came for me,
and there was no one left to speak for me.
Skype, game over.
leveraging an https (URI_introduced) session requires the client using the uRI (e.g. Microsoft) having access to the sessionid of the legitimate client. This is normally not possible, since clients rarely share session id databases
Correctly, one comments that sensitive data is present in the (cleartext) URI, that happens to have an https scheme component. Since the data is in the clear, it was obviously not deemed sensitive by the party citing the Https URI.
The analysis and implied conclusions are bogus.
That Microsoft scans https (but not http) uris in Skype streams in realtime is interesting - from the perspective of trap and trace public policy.
Posted by: peter williams at May 16, 2013 03:38 PMFYI; I tested an http (non-ssl) link and got the standard HEAD ping on it in <3 hours
Posted by: Jon C at May 16, 2013 03:45 PMFrom Full Disclosure list:
http://kirils.org/skype/stuff/pdf/2011/ms_thesis_analysis.pdf
Analysis and detection of Skype network traffic by Luboˇs Pt ́aˇcek
Abstract
This thesis deals with traffic identification of the Skype application. Payload
and flow based analysis of the standby traffic and voice calls is done. Skype
flow patterns are used to create a plugin for NfSen to detect UDP voice calls
in the network.
There is absolutely no reason that users should expect privacy nor security from Skype, under Microsoft ownership or otherwise!
The solution to the concerned is simply a couple of clicks away! In other words, switch from Skype to Jitsi or Pidgin-OTR! From proprietary software to open source, from privacy by policy to privacy by design.
Unfortunately its not only all your skype that belongs to them, but rather all your communications (phone calls, emails, skype, instant messages, facebook, twitter, and pretty much everything cloud). Unless its properly encrypted/decrypted locally and adhering to proper security procedures, you can pretty much assume it belongs to everyone.
Putting it all together presents a gloomy outlook, ECHELON to the power of a hundred or Ratehon's pre-crime RIOT program. Is it our fault that users are negligent and careless for their privacy and security?
The same issue has plagued emails, after all PGP encryption has been out since 1991. Over 20 years later, how many people use it today?
Posted by: Yazid at May 21, 2013 12:40 AMQuote: Elsewhere in his interview with Lake, Greenwald explained that one potential lapse almost led to the loss of the intelligence.
When I was in Hong Kong, I spoke to my partner in Rio via Skype and told him I would send an electronic encrypted copy of the documents, Greenwald said. I did not end up doing it. Two days later his laptop was stolen from our house and nothing else was taken. Nothing like that has happened before. I am not saying its connected to this, but obviously the possibility exists.
Posted by: Skype being used to track Snowden journalist? at June 28, 2013 05:10 AM